CICS/SignOn
CICS/SignOn replaces your old CICS security without costly retraining.
Its user SIGNON and SIGNOFF functions provide seamless integration with your existing CICS signon process.
CICS/SignOn replaces your old CICS security without changes to your existing code.
No source code changes are required. It supports the commands your programming staff uses to determine user identification. Transparently! For example, CICS/SignOn supports EXEC CICS INQUIRE TERMINAL, EXEC CICS ASSIGN commands which return the terminal user's USERID and OPID.
CICS/SignOn replaces your old CICS security without a time-consuming conversion.
Installation time is minimized because the migration to CICS/SignOn is a simple, one step process that takes just a few short minutes. During this process, our migration utilities import your existing transaction, user, and terminal security, while reporting progress and statistics to your administrator.
CICS/SignOn fully supports multi-region operation (MRO) installations.
Your application owning regions (AOR) see the security that the user qualified for when they signed on.
CICS/SignOn results in a much more secure CICS environment.
Unlike the old DFHSNT (table-based) security, your users can change their own passwords without systems programmer intervention and without bringing the CICS region down. More importantly, no one knows the password but the user. The old macro-based security was not secure because systems programmers had to know every password, including the payroll systems password, in order to build signon tables. Worse yet, those passwords were in an assembler source member that anyone could read. Unlike the DFHSNT macros in your source libraries, CICS/SignOn passwords and definitions are encrypted for protection from unauthorized access.
With CICS/SignOn, your administrators can see who is signed on to a particular terminal.
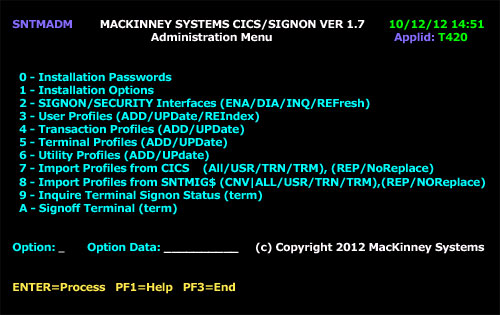
DFHSNT (table/macro-based) security allowed that only with a third party product (like our old WHO's on CICS product). CICS/SignOn provides an online administration tool that's easy to use, rather than DFHSNT (table/macro-based) security that requires scanning source members by hand/eye. You can manage user, terminal and transaction security from a terminal in the affected region.
CICS/SignOn can secure CICS transactions with up to 64 keys.
CICS/SignOn has the ability to define CICS transaction security with multiple keys alleviating much of the need to expand past 64 CICS keys and saving considerable administration time.
CICS/SignOn is centrally controlled.
Passwords may be reset by an authorized system administrator. When a user's password is reset, CICS/SignOn requires that the user change the password the next time the user signs on.
CICS/SignOn keeps track of what it controls.
Had a security breach? A complete audit log of all signons, signoffs, and changes is maintained so you can find the perpetrator and eliminate the problem.
CICS/SignOn saves time.
Because CICS/SignOn secures CICS and nothing more, your systems staff doesn't have to waste time dealing with issues and features that don't have anything to do with CICS. Other security packages affect your entire system even if you only wish to secure CICS.
CICS/SignOn provides user password expiration.
CICS/SignOn provides the ability to require the user to change his password after an administrator-specified number of days.
